By Donna Forbis
I have always been interested in genealogy, an interest I inherited from my grandparents. I also inherited all their family research, which amounts to more than a two-foot by three-foot, four-foot-tall bookcase cabinet can hold! But I love the hunt – searching for that piece of the puzzle that anchors an ancestor in time and place in history. It is because of my interest in genealogy that I was able to fulfill a life-long dream of joining the Daughters of the American Revolution, something I know my grandmother would have loved, but she was unable to find the documentation necessary.
When I was hired for my current position, my love of genealogy was one of the strengths I brought to the job. There is no one else on the staff with the research experience or the knowledge of the inner workings of Ancestry that I have, and my boss has encouraged me to pursue my love of family history through new programming. This led me to standing nervously in front of a small group gathered on a Tuesday morning in January. My biggest fear was that the information I had to impart would not be new, and that the people who were there would leave the library feeling regret that they had wasted an hour they would never get back.
I was not nervous about presenting, in and of itself. I have years of public speaking and performance experience under my belt, and presenting to a crowd, large or small, is something I can do in my sleep. My anxiety was stemming from the idea that, by virtue of leading this series, I am purporting to be an “expert” – someone that others may learn from – but I don’t feel like an expert. I have gotten to this place in my family history journey through benefit of others’ work. If I was starting from scratch, I don’t know that I would know where to begin. My grandparents had laid out a road map when I was very young, and I had simply followed the path they had marked out.
It was this sentiment that helped me focus the subject matter for my first “Digging Deeper into Your Roots” session – “Genealogy 101: Learning How to Climb Your Family Tree.” I realized that I needed to lay out the same road map for those patrons that were coming because they didn’t know where to start. Once I knew where the starting line was, I knew how to explain the journey.
If you watch genealogy TV (and there is a lot of if, from Finding Your Roots to Who Do You Think You Are? to A New Leaf and more), they always start with filling in what you know – your name, date of birth, spouse, marriage date, etc. – then add in all the information you have for your parents and grandparents. An Ancestral Chart is great for doing this. (See photo) It helps focus attention on what information you know and where there are gaps or holes. A basic Ancestral Chart will go back three generations from the starting person, to the starting person’s great-grandparents.

With this information, you are ready to progress to the computer. Websites like Ancestry.com, FamilySearch.com, or MyHertiage.com offer online family trees that are stored in the cloud. Ancestry and MyHeritage require subscriptions, which can be costly. FamilySearch is free, as long as you don’t mind sharing the information you upload with all other users. There are many different genealogy software programs available, as well. These allow users to build a digital family tree, while keeping any or all the information they gather on their home computer. As with the other options, there are pros and cons with this. Should your computer crash or malfunction, all research may be lost, unless it is backed up in another location. Conversely, doing the research yourself minimizes the crowd-sourced information available from online sources.
Crowd-sourced information can be both a blessing and a curse. Amateur genealogists fall into one of two categories – those who are diligent about doing their research and plodding on methodically until they have the information they are looking for, and those that are simply trying to fill in any holes they may have on their family tree by “cutting and pasting” information from wherever they find it. It is this latter group that can be the source of numerous headaches for those just starting out. If one person has incorrect information on their tree AND they share their tree with others, then that incorrect information can spread like wildfire. I have seen “hints” come up with a name misspelled, or a wrong date, or some other piece of misinformation, and then have that same error multiplied across multiple family trees. In the genealogy world, it doesn’t count if you don’t have the documentation to back it up.
I had planned on presenting for about 30-40 minutes, then using the rest of the hour for questions. I took 45 minutes. Our little band continued with questions and discussion for almost as long as I had initially spoken, and as we were closing in on the 90-minute mark, I knew we needed to wrap up. Those in attendance were thrilled that the power point had given them a broad base of information, enough for them to get started. I was thrilled that I hadn’t made a complete fool out of myself.
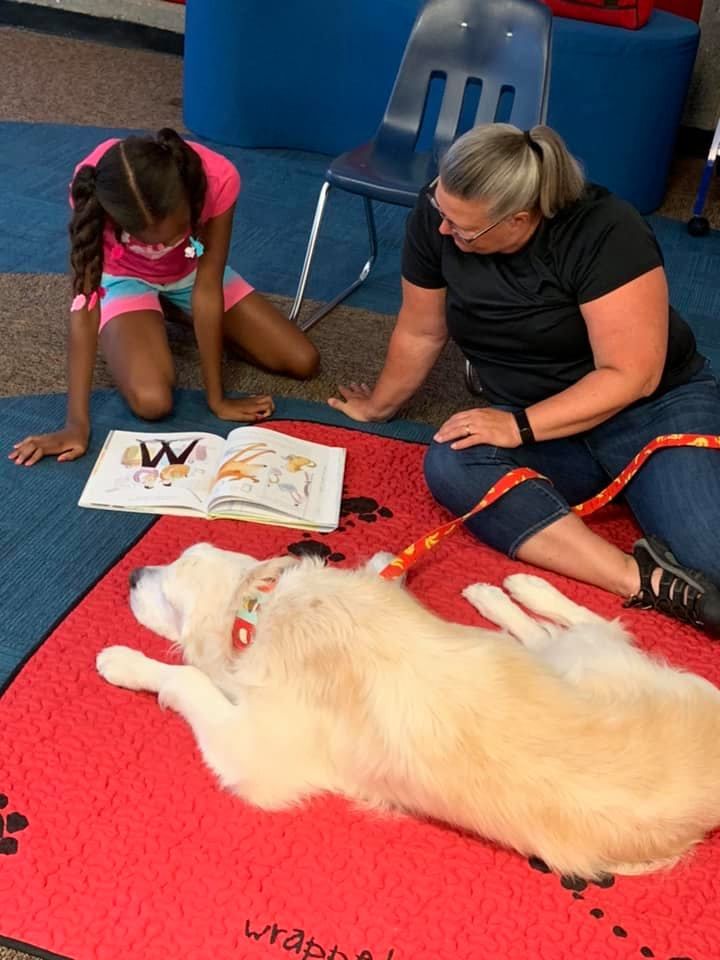
As I write this, I am working on my program for February – “Tombstone Tourism” – on doing cemetery research, and again, I am grateful for the work of other experts from which to draw information. I still don’t feel like an expert, but I know that part of the reason genealogy has become so popular of late is that it is a collaborative effort. In an age of digital isolation – communication with others through social media, texting, and email – working together for a common goal is a novel experience. We are reaching into the past to connect with ancestors we never knew before, and, in doing so, we are reaching one another and making new connections that we would otherwise never have.